Beneath the Surface: Unveiling Steganography in Wildlife Law Enforcement

What is Steganography: In digital terms Steganography is a technique of concealing informations/data within other media such as image, video, audio & text file. Unlike cryptography which encrypts data to secure its content by making it unreadable, Steganography hides the very existence of the data by making it covert. It can be used for both legitimate and illegitmate purposes. It can be used as a medium for secure communication of sensitive informations by security agencies or by individuals for data privacy. Criminal actors including wildlife traffickers can also use this clandestine technique for carrying out their illicit activities. QuickStego, OpenStego, Steghide, SteganoG, OutGuess, DeepSound etc. are some of the Steganography tools.
.png)
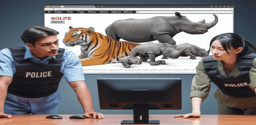
Weaponization of Steganography by Wildlife Criminals: In modern digital technology-driven world, wildlife traffickers are employing sophisticated techniques to evade detection and carry out their illicit activities with a sense of impunity. One of such techniques that can be weaponized by the wildlife traffickers to further their illicit activities is Steganography technique. Wildlife criminals may use Steganography technique to their advantages in folowing ways:
- Using Steganography, wildlife traffickers can obscure the incriminating evidences regarding poaching/hunting, details of illegal wildlife trade including wildlife contrabnds already illeglly traded by them, buyers of wildlife contrabands and their addresses, payment details, details of Bank Accounts or Crypto-Exchanges/Crypto-Wallets used for receiving sale proceeds in fiat currency or cryptocurrencies, details of their accomplices in wildlife trafficking, details of their investments of proceeds of illegal wildlife trade, details of social media & e-commerce and online forums etc. being used by them for illegal trade, '.onion URLs' if they are operating on Darkent etc. within seemingly innocuous images, audio files, video files etc. Thus using Steganography tools, wildlife criminals can mask their illicit activities in plain sight.
- Members of the wildlife crime syndicates can communicate with each other and coordinate their illicit activities in a secure manner by embedding messages within image, audio or video files.
Let me explain how willdife traffickers may use Steganography techniques to hide incriminating evidences behind an image using QuickStego tool:
.png)
Suppose the wildlife trafficker wants to hide the details of sale of wildlife contrabands within an image of flowers as shown below:
.png)
The wildlife trafficker may simply open the QuickStego Steganography tool and upload the image of flowers and text file containing details of sale of willdife contrabands and hide this incriminating data within this image of flowers as shown below:
.png)
Once the image is saved, incriminating data of sale of wildlife contrabands will be embedded and hidden wihin the image. The wildlife trafficker can share this data with his other accomplices just by sharing this image securely.
How Wildlife Law Enforcement can Counter Challenges posed by Steganography: Following measures will be required to counter the formidable challenges posed by this clandestine technique:
- Specialized tools and expertise are required to detect the steganographically hidden incriminating data. Wildlife law enforcement officials must be imparted training to understand how Steganography works, the various methods of Steganography, signs of files containing hidden incriminating data etc.
- Wildlife law enforcement agencies must be equipped with the advanced forensic tools capable of detecting steganographically hidden incriminating data and analyzing various file formats i.e. text, image, audio, video etc. used for hiding data. StegExpose, StegSecret, StegDetect, QuickStego etc. are some of the tools that can be used to detect and unmask the hidden data.
In a nutshell, to counter the dangerous convergence of Wildlife Trafficking and Steganography requires upgradation of technologicall skillsets of law enforcement agencies. Equipped with these technological skillsets, law enforcement officials can infiltrate into the underworld of hidden data, extract the incriminating evidences against the wildlife criminals and bring them to justice in their pursuit of dismantling the wildlife trafficking syndicates.




Please sign in or register for FREE
If you are a registered user on WildHub, please sign in